Cyber Security Principles
Cyber Security Principles
Guiding Principles are aspirational, developed and delivered as a partnership between Government and ISPs.
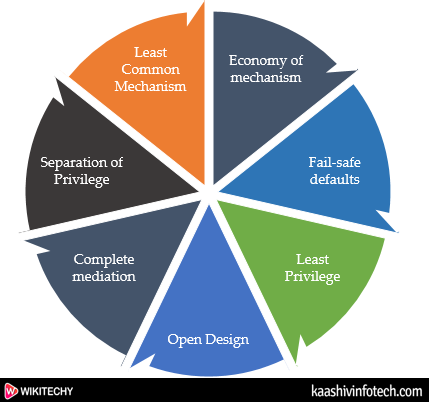
Some of the essential cyber security principles are -
Cyber Security Principles
- Economy of mechanism
- Fail-safe defaults
- Least Privilege
- Open Design
- Complete mediation
- Separation of Privilege
- Least Common Mechanism
- Psychological acceptability
- Work Factor
- Compromise Recording
Economy of mechanism
- The Economy of mechanism principle simplifies the design and implementation of security mechanisms.
- The checking and testing process is less complicated so that fewer components need to be tested.
- Interfaces between security modules are the suspect area which should be as simple as possible.
Fail-safe defaults
- Fail-safe defaults principle states that the default configuration of a system should have a conservative protection scheme.
Least Privilege
- Principle states that a user should only have those privileges that need to complete his task.
- If possible, the elevated rights of a user identity should be removed as soon as those rights are no longer needed.
Read Also
Open Design
- Principle states that the security of a mechanism should not depend on the secrecy of its design or implementation.
Complete mediation
- The principle of complete mediation restricts the caching of information, which often leads to simpler implementations of mechanisms.
- The operating system should mediate all and every access to an object.
Separation of Privilege
- This principle states that a system should grant access permission based on more than one condition being satisfied.
- Two conditions must be met -
- The user must know the root password.
- The user must be in the right group (wheel).
Least Common Mechanism
- This principle may also be restrictive because it limits the sharing of resources.
Psychological acceptability
- The psychological acceptability principle recognizes the human element in computer security.
- If security-related software or computer systems are too complicated to configure, maintain, or operate, the user will not employ the necessary security mechanisms.
Work Factor
- This principle states that the cost of circumventing a security mechanism should be compared with the resources of a potential attacker when designing a security scheme.
Compromise Recording
- Compromise Recording principle states that sometimes it is more desirable to record the details of intrusion that to adopt a more sophisticated measure to prevent it.
