Cyber Security Technology
Security Technologies
Cyber Security Technologies
Firewall
- Firewall is a computer network security system designed to prevent unauthorized access to or from a private network.
- Firewalls are used to prevent unauthorized Internet users from accessing private networks connected to the Internet.
Categories of Firewalls
Firewall categorized into the following types-
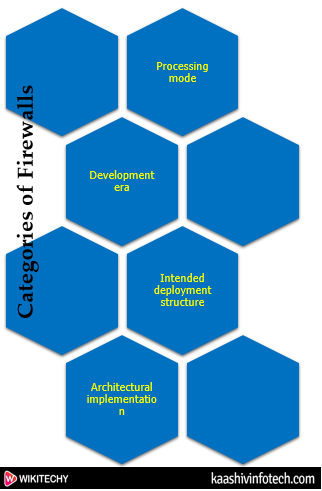
Cyber Security Firewall Categories
Processing mode
- The five processing modes that firewalls can be categorized are-
Packet filtering
- Packet filtering firewalls examine header information of a data packets that come into a network. Most firewall often based on a combination of:
- Internet Protocol (IP) source and destination address.
- Direction (inbound or outbound).
- Transmission Control Protocol (TCP) or User Datagram Protocol (UDP) source and destination port requests.
- Packet filtering firewalls three types-
- Static filtering: These filtering rules governing how the firewall decides which packets are allowed and which are denied are developed and installed.
- Dynamic filtering: It allows the firewall to set some rules for itself, such as dropping packets from an address that is sending many bad packets.
- Stateful inspection: A stateful firewalls keep track of each network connection between internal and external systems using a state table.
Application gateways
- This firewall proxy filters incoming node traffic to certain specifications that mean only transmitted network application data is filtered. Such network applications include FTP, Telnet, Real Time Streaming Protocol (RTSP), BitTorrent, etc.
Circuit gateways
- A circuit-level gateway is a firewall that operates at the transport layer. It provides UDP and TCP connection security which means it can reassemble, examine or block all the packets in a TCP or UDP connection.
MAC layer firewalls
- MAC addresses of specific host computers are linked to the access control list (ACL) entries. This entry identifies specific types of packets that can be sent to each host and all other traffic is blocked
Hybrid firewalls
- It is a combine feature of other four type of firewalls. These are elements of packet filtering and proxy services, or of packet filtering and circuit gateways.
Development Era
- Firewall on the basis of the generation type. These are
- First Generation
- Second Generation
- Third Generation
- Fourth Generation
- Fifth Generation
First Generation
- The first generation firewall comes with static packet filtering firewall. A static packet filter is the simplest and least expensive forms of firewall protection.
Second Generation:
- Second generation firewall comes with Application level or proxy servers. This generation of firewall increases the security level between trusted and untrusted networks. This program evaluates data sent from the client and decides which to move on and which to drop.
Third Generation
- The third generation firewall comes with the stateful inspection firewalls. This generation of the firewall has evolved to meet the major requirements demanded by corporate networks of increased security while minimizing the impact on network performance.
Fourth Generation
- The fourth generation firewall comes with dynamic packet filtering firewall.
Fifth Generation
- The fifth generation firewall comes with kernel proxy firewall. This firewall works under the kernel of Windows NT Executive.
Intended deployment structure
- Firewall categorized based on the structure. These are-
- Commercial Appliances
- Small Office Home Office
- Residential Software
Commercial Appliances
- It runs on a custom operating system. This firewall system consists of firewall application software running on a general-purpose computer.
Small Office Home Office
- The SOHO firewall is designed for small office or home office networks that need protection from Internet security threats.
- A firewall for a SOHO (Small Office Home Office) is the first line of defense and plays an essential role in an overall security strategy.
Residential Software
- Residential-grade firewall software is installed directly on a user's system.
- Some of these applications combine firewall services with other protections such as antivirus or intrusion detection.
Architectural Implementation
- The objectives of the network, the organization's ability to develop and implement the architectures, and the budget available for the function.
- There are four common architectural implementations of firewalls:
- Packet-filtering routers
- Screened host firewalls
- Dual-homed host firewalls
- Screened Subnet Firewalls
Packet-filtering routers
- Packet filtering firewall is used to control the network access by monitoring the outgoing and incoming packets.
Screened host firewalls
- This firewall architecture combines the packet-filtering router with a separate and dedicated firewall. The application gateway needs only one network interface.
Read Also
Dual-homed host firewalls
- The Implementation of this architecture often makes use of NAT. NAT is a method of mapping assigned IP addresses to special ranges of no routable internal IP addresses, thereby creating another barrier to intrusion from external attackers.
Screened Subnet Firewalls
- This architecture adds an extra layer of security to the screened host architecture by adding a perimeter network that further isolates the internal network from the Internet.
VPNs
- A VPN stands for virtual private network. It is a technology which creates a safe and an encrypted connection on the Internet from a device to a network.
Intrusion Detection System (IDS)
- An IDS is a security system which monitors the computer systems and network traffic. It analyses that traffic for possible hostile attacks originating from the outsider and also for system misuse or attacks originating from the insider. Intrusion Detection System have different types to detects the suspicious activities are
- NIDS
- HIDS
- Signature-based Intrusion Detection System
- Anomaly-based Intrusion Detection System
NIDS
- It is a Network Intrusion Detection System which monitors the inbound and outbound traffic to and from all the devices over the network.
HIDS
- It is a Host Intrusion Detection System which runs on all devices in the network with direct access to both internet and enterprise internal network. It can detect anomalous network packets that originate from inside the organization or malicious traffic that a NIDS has failed to catch.
Signature-based Intrusion Detection System
- It is a detection system which refers to the detection of an attack by looking for the specific patterns, such as byte sequences in network traffic, or known malicious instruction sequences used by malware.
Anomaly-based Intrusion Detection System
- This detection system primarily introduced to detect unknown attacks due to the rapid development of malware. It alerts administrators against the potentially malicious activity.
Access Control
- Access control is a process of selecting restrictive access to a system. It is a concept in security to minimize the risk of unauthorized access to the business or organization. The access control can be categories into two types:
- Physical Access Control- This type of access control limits access to buildings, rooms, campuses, and physical IT assets.
- Logical access control- This type of access control limits connection to computer networks, system files, and data.
- The access control consists of two main components: authorization and authentication.
- Authentication is a process which verifies that someone claims to be granted access.
- Authorization provides that whether a user should be allowed to gain access to a system or denied it.
